Whilst governments and corporations have fortified their defenses against cyber threats in recent years, most individuals and families remain woefully unprepared and vulnerable.
Increasingly, cybersecurity is something most of us should think about every day.
The unfortunate reality of our modern world is that locally and internationally based individuals, criminal organisations and (most menacing of all) a number of state actors are investing considerable energy and expertise every day to spy on – and steal from – each and every one of us. And every day, they’re becoming more and more sophisticated in the way they do it.
What are they after? They’re after our digital assets!
Protecting your digital assets
Anything you own or have rights to that is accessed online is a digital asset. This includes photos, videos, access to bank accounts and investment funds, email, social media accounts, websites, scanned documents, online medical information, online financial information, shopping accounts plus more. Confidential information is the main target of cybercriminals, including medical, financial or personal data. However, cybercriminals will pick up any information they can find on a person as a means to impersonate them to gain access to their confidential information. For this reason, it is important that precautions are taken, and protections are put in place for all of your digital assets, even if you think it is not so important. You are only as strong as your weakest link.
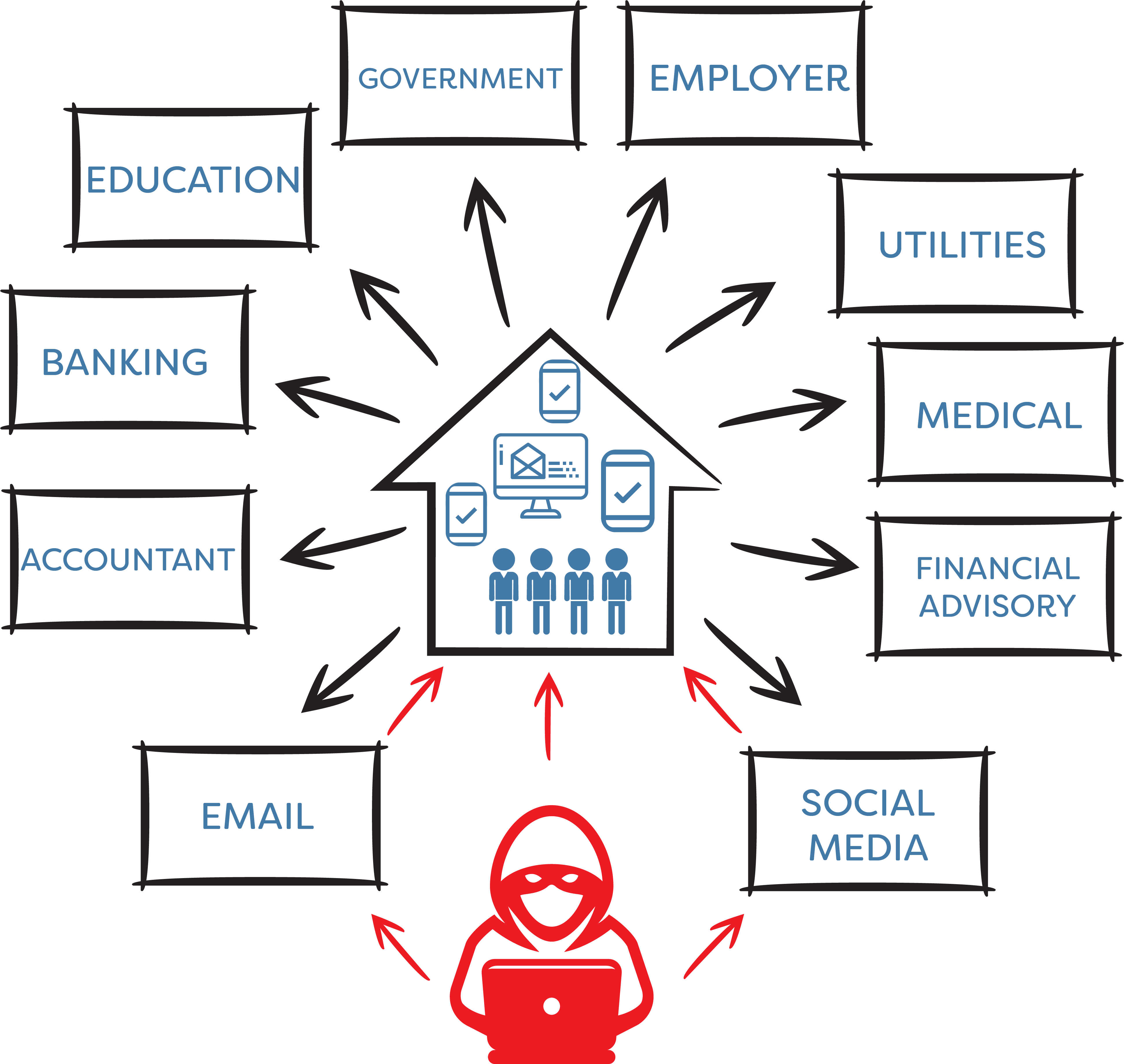
As a financial advisory firm, we have been aware for many years of the importance of vigilance when it comes to the protection of client data and client assets. In fact, we routinely stress-test our infrastructure and ensure that we have appropriate digital and human protections in place at all times. But it’s critical our clients put in place their own layers of protection too. Organisations and institutions that handle your confidential information tend to build virtually impenetrable systems and procedures to protect your data. For this reason, cybercriminals tend to take the easier route of hacking emails and social media accounts to impersonate individuals and families in order to access confidential data housed by external bodies, as represented in the below graphic.
So, what can you do to better protect your digital assets? The reality is that cybercriminals are becoming more advanced in the way they work. Our first recommendation is to keep cybersecurity front of mind always, be vigilant and be smart in what you do online. Furthermore, we recommend taking some more proactive measures, including:
• Understand if any of your data has been subject to a known data breach (you can easily check this via haveibeenpwned.com).
• Take password selection and management very seriously; this includes not using the same password for multiple accounts, ensuring your passwords are strong and considering the use of a password manager (Stay Smart Online has further information on password security).
• Use two-factor authentication on all sites containing sensitive information (such as banking and other financial information).
• Consider using a Virtual Private Network (VPN) whenever you’re online. This Forbes article discusses what a VPN is as well as some of the features and benefits of VPNs.
• Consider your online behaviour, but also the behaviour and vigilance of others in your family or those who access your home network (or Wi-Fi).
Protecting your digital legacy
We live in an era where much of our communication and activity takes place online, our photos and videos are stored digitally, and important documents and certificates are scanned for safe keeping. Think about everything you own digitally – photos, videos, emails, letters, scanned documents, electronic receipts, certificates. What monetary, legal, historic or sentimental value do these items hold? Now think about what might happen to all of this when you’re gone. What will happen to your digital legacy? While one might assume that these items will automatically form part of their estate and will be passed on to executors or children, it’s not necessarily the case.
When reviewing your estate plan more generally, we recommend you identify and incorporate the main components of your digital life which may include passwords, online financial-related accounts, email and social media accounts as well as other digital assets such as photos or videos. We suggest including instructions on how to access these assets and how to distribute them in your estate plan.
We’re busy revising our estate planning guidelines, which details how we deal with estate planning professionals on behalf of our clients, and digital legacy will form part of this. We’re also in the process of exploring advice and solutions for our clients with respect to data and cybersecurity and will be hosting a number of educational sessions that outline what you need to do to ensure your data in protected across all platforms. If you’re interested in learning more about this, please get in touch with us via update@mgdwealth.com.au. If you have any cybersecurity related concerns or questions, or queries related to estate planning more broadly, we encourage you to get in touch with your adviser or our office.
Disclaimer: This article contains general information only and is not intended to constitute financial product advice. Any information provided or conclusions made, whether express or implied, do not take into account the investment objectives, financial situation and particular needs of an investor. It should not be relied upon as a substitute for professional advice.

